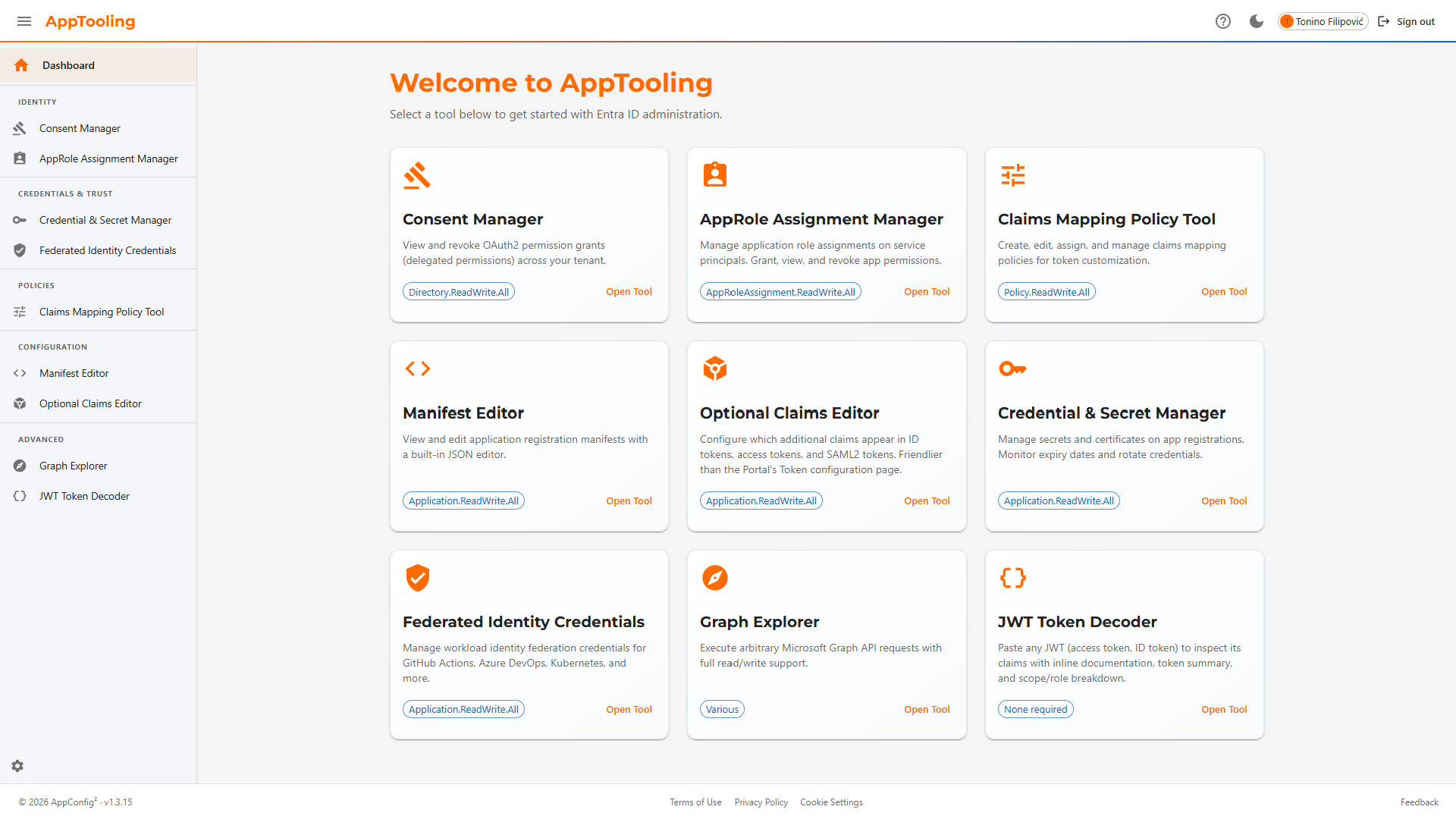
Why AppTooling?
The Azure Portal is great for one-off changes through its UI, and PowerShell/CLI scripts are ideal for fully automated pipelines. AppTooling targets the gap in between: privileged, interactive Entra ID administration tasks that require judgment and confirmation — performed through a purpose-built interface with guardrails built in.
No Portal Context-Switching
Consent cleanup, role assignments, and credential rotation — all in one interface instead of navigating across multiple Portal blades.
Confirmation on Every Write
Every DELETE, PATCH, and POST operation requires explicit confirmation. Mistakes are surfaced before they happen, not after.
Guided Operations
Templates for workload identity federation, a curated optional claims catalog, and built-in schema validation eliminate error-prone manual JSON editing.
Nine Focused Tools
Organised into four functional areas covering the full scope of Entra ID application administration.
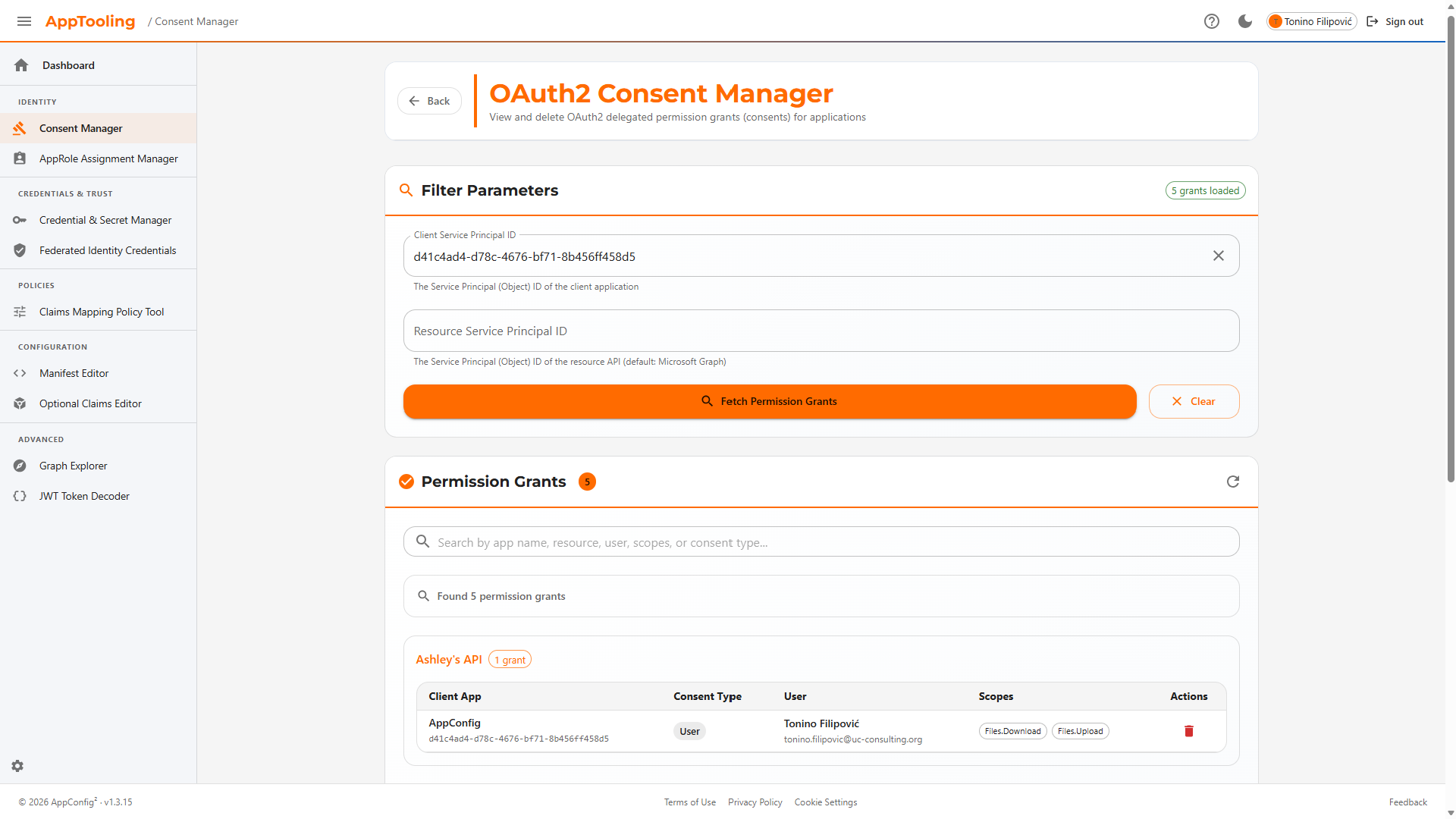
Consent Manager
List all OAuth 2.0 delegated permission grants in the tenant. Filter by client or resource service principal. Revoke individual grants with a confirmation step. Distinguishes admin consent (AllPrincipals) from user consent (Principal) and surfaces the granting user's UPN.
Required: Directory.ReadWrite.All
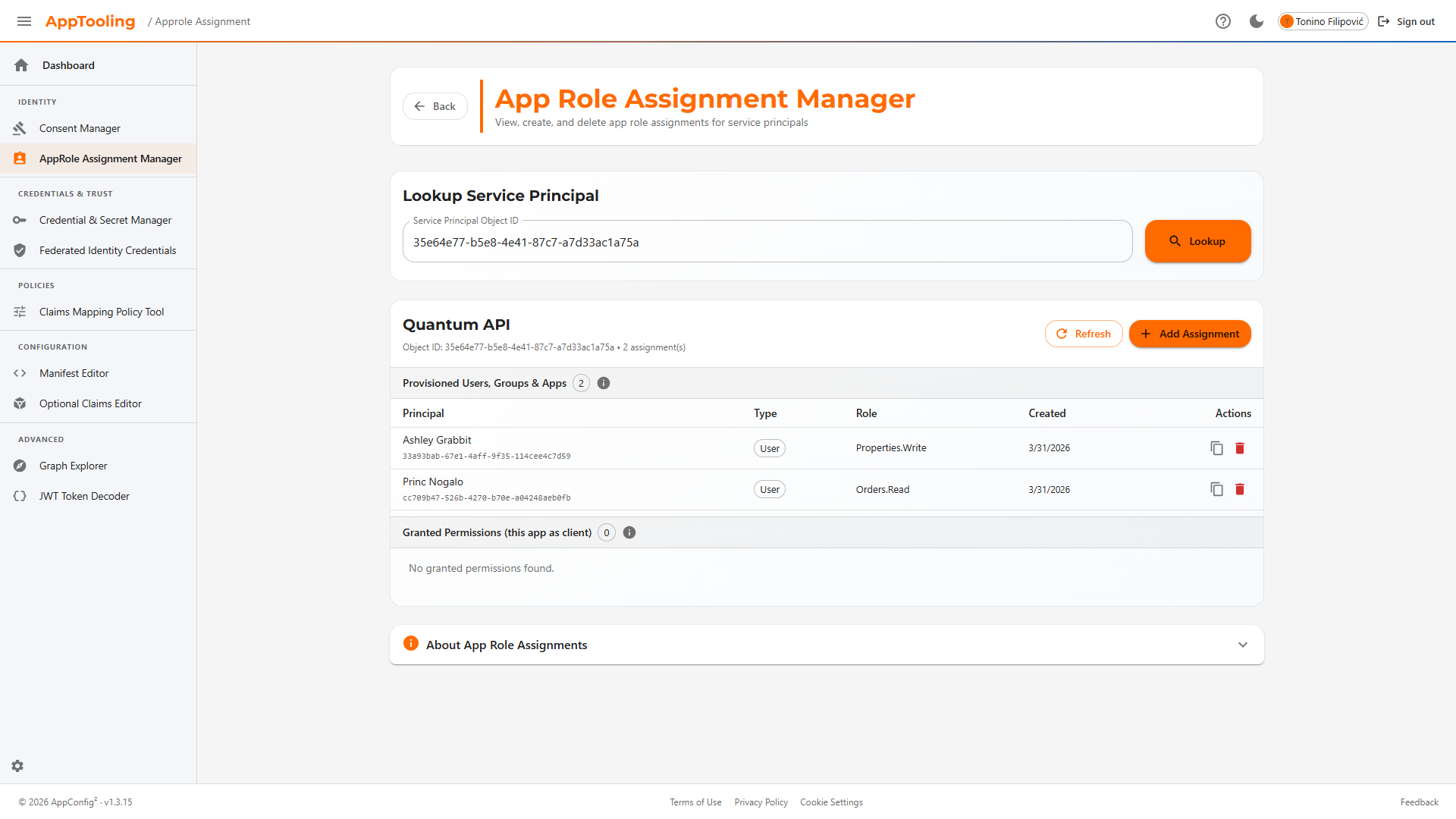
AppRole Assignment Manager
View app role assignments from both the principal's perspective (appRoleAssignments) and the resource's perspective (appRoleAssignedTo). Create new assignments by searching for service principals and selecting from their exposed app roles. Delete with confirmation.
Required: AppRoleAssignment.ReadWrite.All
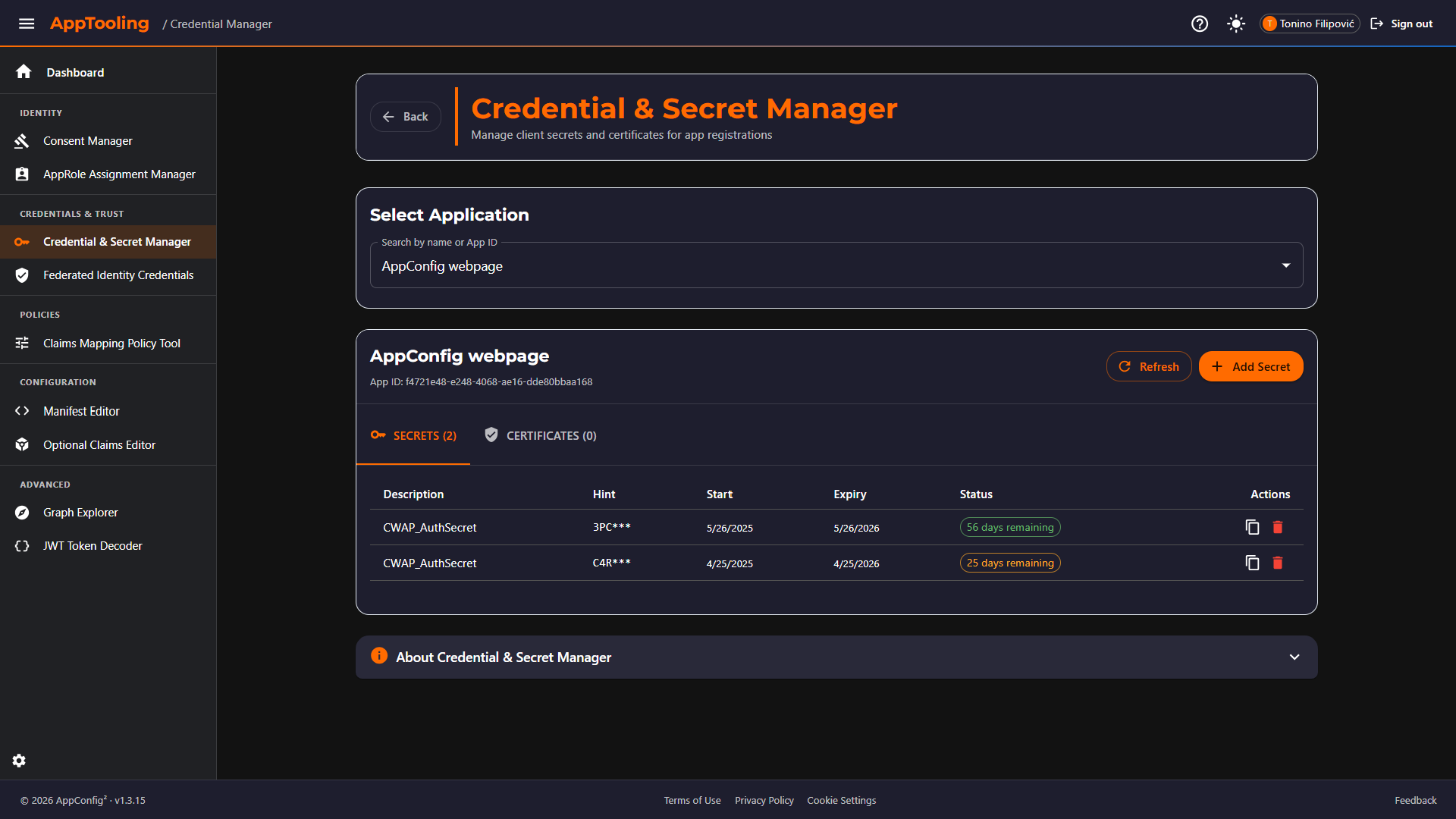
Credential & Secret Manager
Browse all client secrets and certificates across app registrations with colour-coded expiry status (configurable warning threshold). Create new secrets with configurable default lifetime. Certificates display thumbprint, type, and usage. New secret values are shown exactly once at creation.
Required: Application.ReadWrite.All
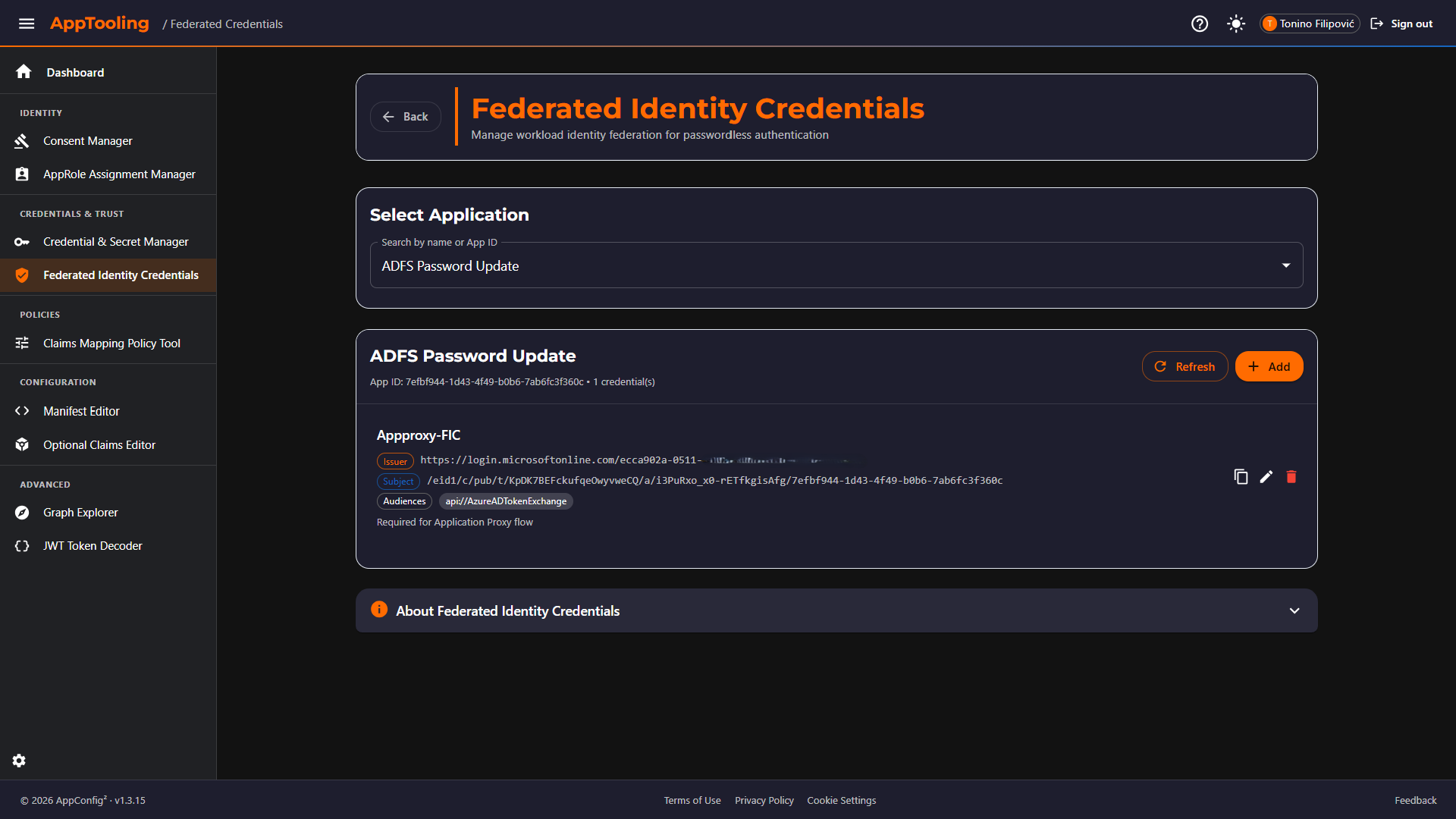
Federated Identity Credentials
Create and manage workload identity federation (WIF) credentials. Guided templates eliminate manual subject construction for the four most common issuers: GitHub Actions (branch / environment / PR), Azure DevOps, Kubernetes (service account), and Google Cloud. Custom issuers are also supported.
Required: Application.ReadWrite.All
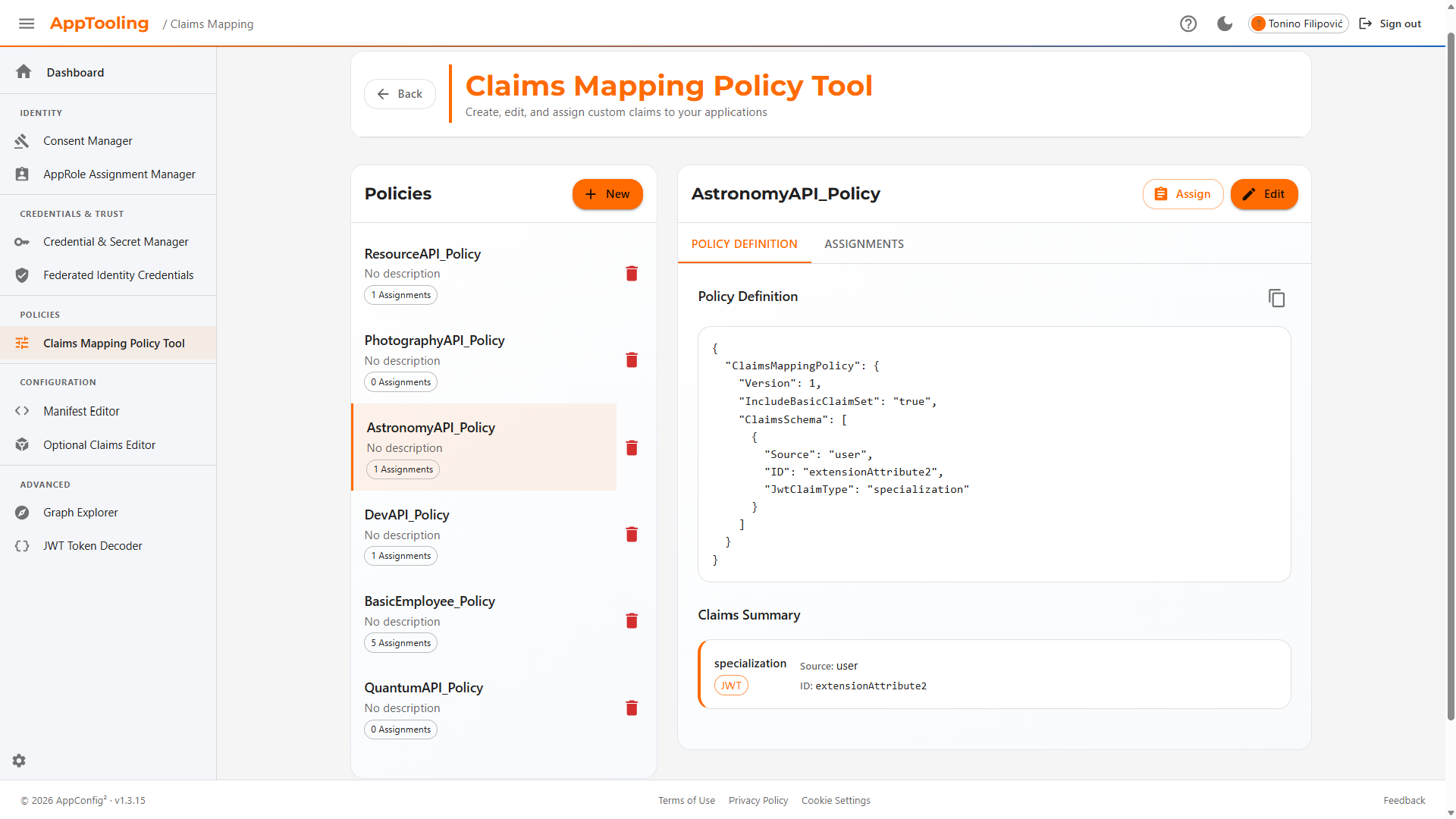
Claims Mapping Policy Tool
Full CRUD for claimsMappingPolicy objects. Built-in templates cover the most common customisations: department, employee ID, job title, extension attributes, group claims, and SAML name identifier. JSON editor with schema validation. Assign and unassign policies to service principals without leaving the tool.
Required: Policy.ReadWrite.ApplicationConfiguration
Manifest Editor
Search any application registration and load its manifest in a syntax-highlighted JSON editor. Edit and save using Graph's JSON Merge Patch semantics. Displays app type chips (Web / SPA / Native / multi-tenant). Diff-detects unsaved changes and prompts before navigation.
Required: Application.ReadWrite.All
Optional Claims Editor
Configure optionalClaims (ID token, access token, SAML2 token) through a structured UI backed by a curated claim catalog. Each claim includes a plain-language description, supported token types, and available additionalProperties. Changes are diffed against saved state and can be reverted before saving.
Required: Application.ReadWrite.All
Graph Explorer
Execute arbitrary Microsoft Graph REST calls (GET / POST / PATCH / DELETE) against v1.0 or beta. Auto-detects required scopes per endpoint and triggers just-in-time consent. Syntax-highlighted JSON response panel with status code display. Built-in JWT decoder for the current session token. Common endpoint suggestions with scope hints.
Varies — JIT consent per endpoint
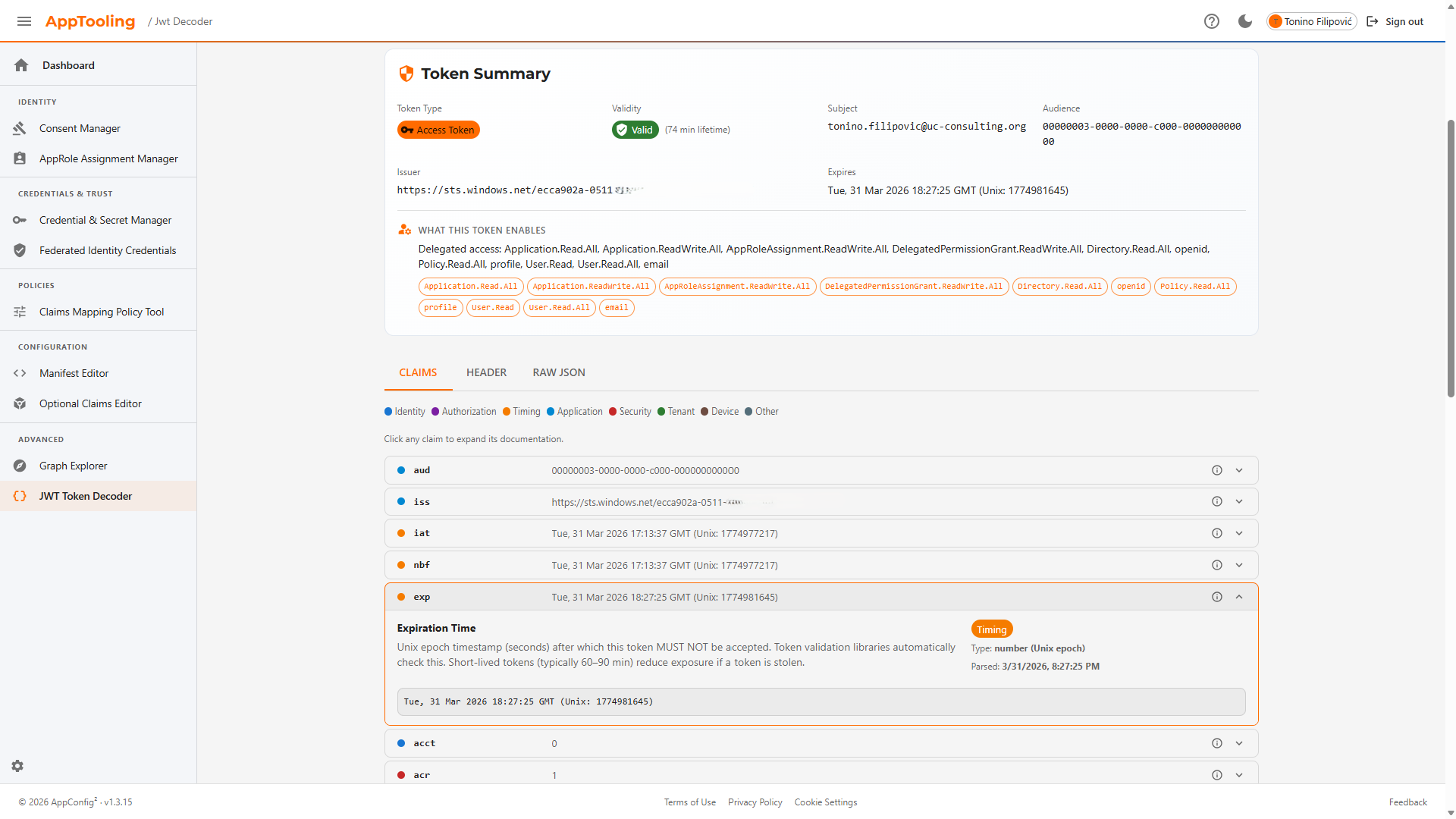
JWT Token Decoder
Paste any JWT (access token, ID token, or custom token) for a fully annotated breakdown. Auto-detects token type and validity (valid / expired / not-yet-valid). Token Summary shows type, expiry, subject, audience, issuer, lifetime in minutes, and a plain-English scope and app-role summary. Claims tab renders every claim with a colour-coded category dot (Identity, Authorization, Timing, Application, Security, Tenant, Device) — click any claim to expand its documentation and a Microsoft Docs link. Header and Raw JSON tabs also available. Decoding is entirely client-side; no Graph calls are made.
Required: None — client-side only
Key Capabilities
Consent Lifecycle
List, filter, and revoke OAuth 2.0 delegated permission grants. See exactly which users granted consent and to which resources.
Workload Identity Federation
Guided templates for GitHub Actions, Azure DevOps, Kubernetes, and Google Cloud. Eliminate long-lived secrets for CI/CD and service workloads.
Manifest Editing
Load, edit, and save application manifests with a JSON Merge Patch workflow. Diff detection prevents accidental overwrites.
Optional Claims (Structured UI)
Configure optional claims for ID, access, and SAML2 tokens through a structured UI with a curated catalog — no raw JSON required.
Credential Management
Browse client secrets and certificates across app registrations with expiry alerts. Create secrets with configurable lifetimes; values shown once only.
Claims Mapping Policies
Full CRUD for claimsMappingPolicy objects with built-in templates and SP assignment — without hand-editing JSON policy documents.
Who is AppTooling for?
Purpose-built for roles that need privileged Entra ID operations with guardrails.
Entra ID Admins
Day-to-day consent cleanup, role assignments, and credential rotation without navigating multiple Azure Portal blades.
DevSecOps Engineers
Configure workload identity federation for GitHub Actions, Azure DevOps, and Kubernetes — eliminating long-lived secrets from pipelines.
Identity Architects
Configure claims mapping policies and optional claims for custom token shapes without hand-editing raw JSON policy documents.
Developers
Inspect application manifests, test Graph API calls interactively with live JWT decoding, and validate optional claims behaviour end-to-end.
Security & Compliance
Audit and revoke OAuth consent grants. Monitor credential expiry across all app registrations. Evidence-based compliance reporting.
Cloud Architects
Design and validate token customisation strategies, workload identity trust chains, and application permission models at scale.
Security-First Design
AppTooling is a write-capable tool. Every security decision was made to prevent accidental or malicious misuse — without getting in the way of legitimate administration.
Authentication & Authorization
- MSAL Authorization Code Flow with PKCE — no implicit flow, no client secrets in the browser
- Single-tenant enforcement — only accounts from the configured Entra ID tenant can sign in
- sessionStorage cache — sessions are isolated per browser tab, not shared across tabs
- JIT scope consent — Graph permissions are requested on demand per tool, not upfront
- Silent sign-out — uses the
login_hintoptional claim to avoid extra server round-trips
OWASP Client-Side Controls
- X-Frame-Options: DENY — blocks clickjacking attacks
- X-Content-Type-Options: nosniff — prevents MIME-type sniffing
- Referrer-Policy: strict-origin-when-cross-origin
- Permissions-Policy — restricts camera, microphone, geolocation
- Security headers applied at SWA layer — via
staticwebapp.config.json
Write Operation Guardrails
- Confirmation dialogs on every write (DELETE / PATCH / POST) — no silent mutations
- Secrets shown once — new credential values are displayed immediately after creation and cannot be retrieved again
- Unsaved changes detection — Manifest Editor and Optional Claims Editor prompt before navigation away
- No client-side secret storage — no secrets or tokens written to localStorage beyond short-lived Graph response caches
Infrastructure & Data Residency
- Fully static SPA — no server-side code, no backend, no data processed outside Microsoft's infrastructure
- Azure Static Web Apps hosting — all requests go directly from the browser to Microsoft Graph
- In-memory + localStorage caching of Graph responses with short TTLs (5–30 min) to reduce redundant API calls
- No telemetry or third-party analytics beyond what Azure SWA platform collects
How AppTooling Fits the Suite
AppTooling is complementary to the other tools — it covers a distinct set of administrative operations not addressed elsewhere in the suite.
| Dimension | AppConfig | AppTesting | AppDashboard | AppTooling |
|---|---|---|---|---|
| Write capable? | ||||
| Authentication flow testing | ||||
| Tenant-wide analytics & security scoring | ||||
| Consent Manager (OAuth grant audit & revoke) | ||||
| Workload Identity Federation / Federated Credentials | ||||
| AppRole Assignment Manager | ||||
| Application Manifest Editor (JSON Merge Patch) | ||||
| Optional Claims Editor (structured UI) | ||||
| Graph Explorer |
Ready to Streamline Your Entra ID Administration?
Get AppTooling as part of the AppConfig² Suite on Azure Marketplace
Get Started on Azure Marketplace Explore the Full SuiteQuestions About AppTooling?
Want to learn more or report an issue? Our team is here to help.